SEANux 1.0 remote code execution Vulnerability
Larry W. Cashdollar, @_larry0
1/23/2015
The SEA stated that this distribution is not to be used as a server, in order to secure network connections against port 80, modify the apache configuration to bind to localhost:80. This is a misconfiguration and will be fixed in the next release.
Remote PoC: Here
Modify ports.conf in the following way:
# cat ports.conf |grep -n 127
8:NameVirtualHost 127.0.0.1:80
9:Listen 127.0.0.1:80
This will prevent general network access to the scripts pre-loaded in the web root, but won't help with Javascript payloads embedded in webpages like the PoC I provided above.
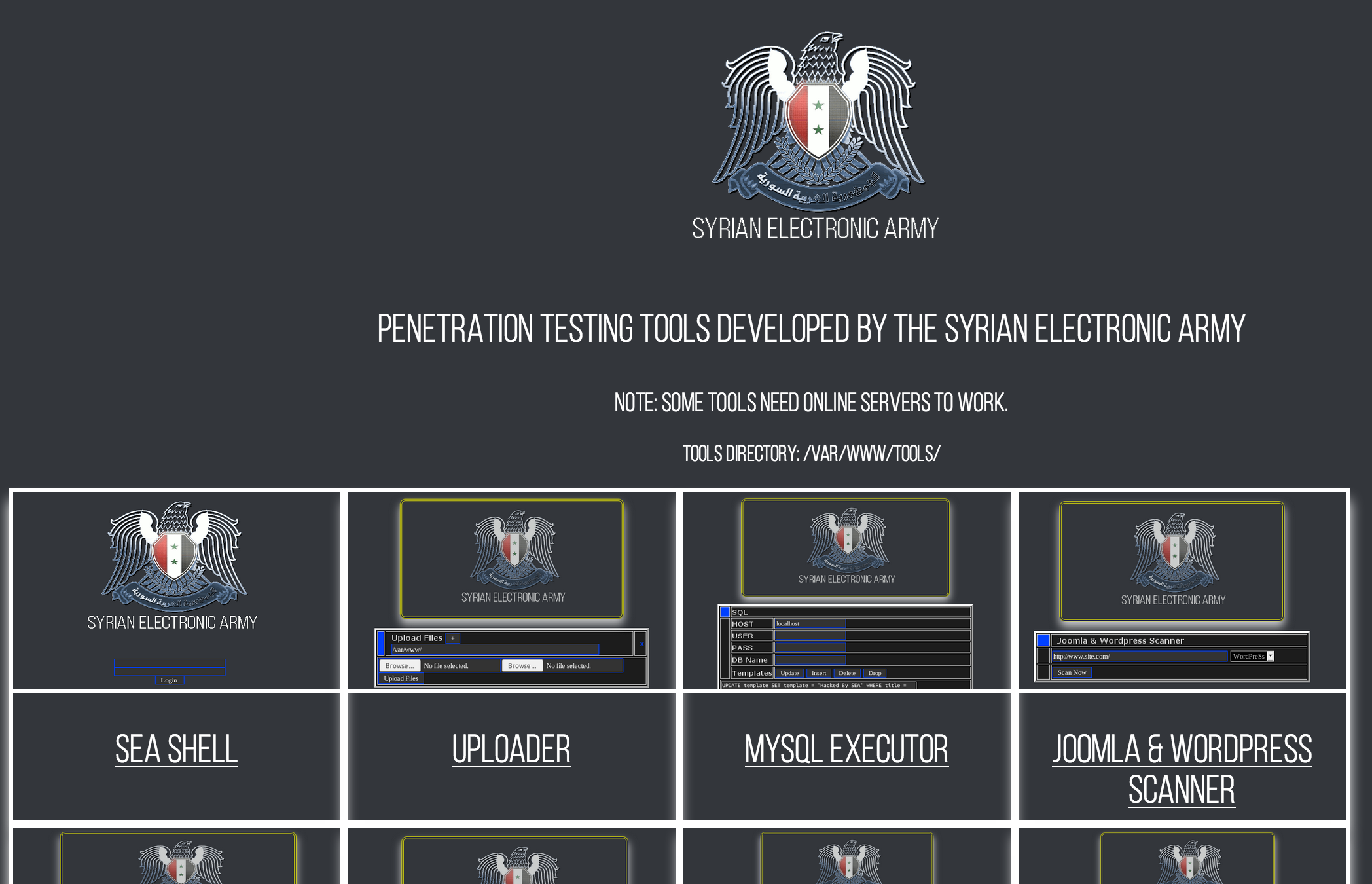
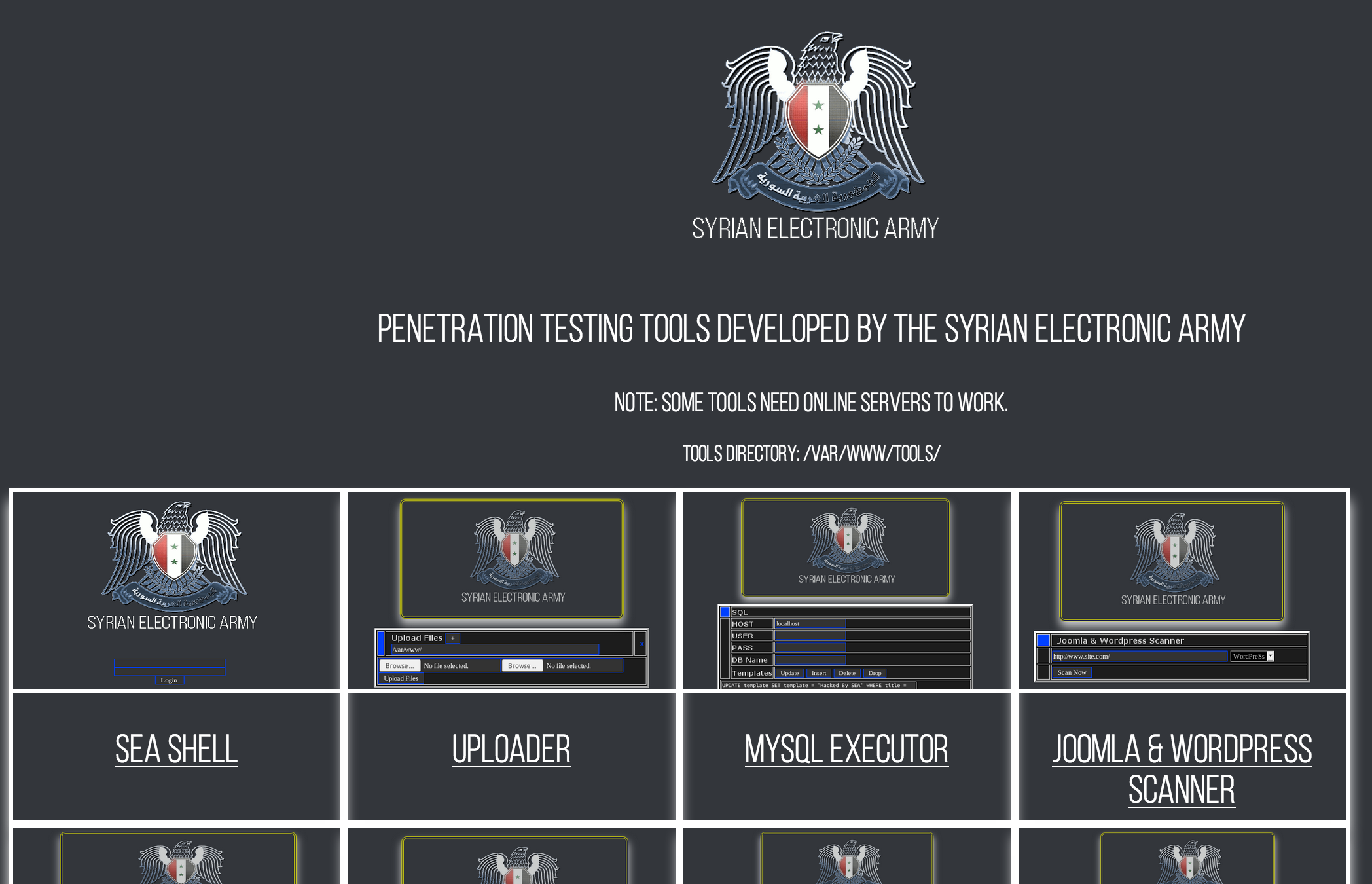
SEANux 1.0 is a linux distribution Available here developed by the Syrian Electronic Army.
The SEA pre-populated the distribution with some of their home grown tools under /var/www.
The tools appear to be developed in PHP & Perl and are web based. They are served through a local apache instance running on the desktop system
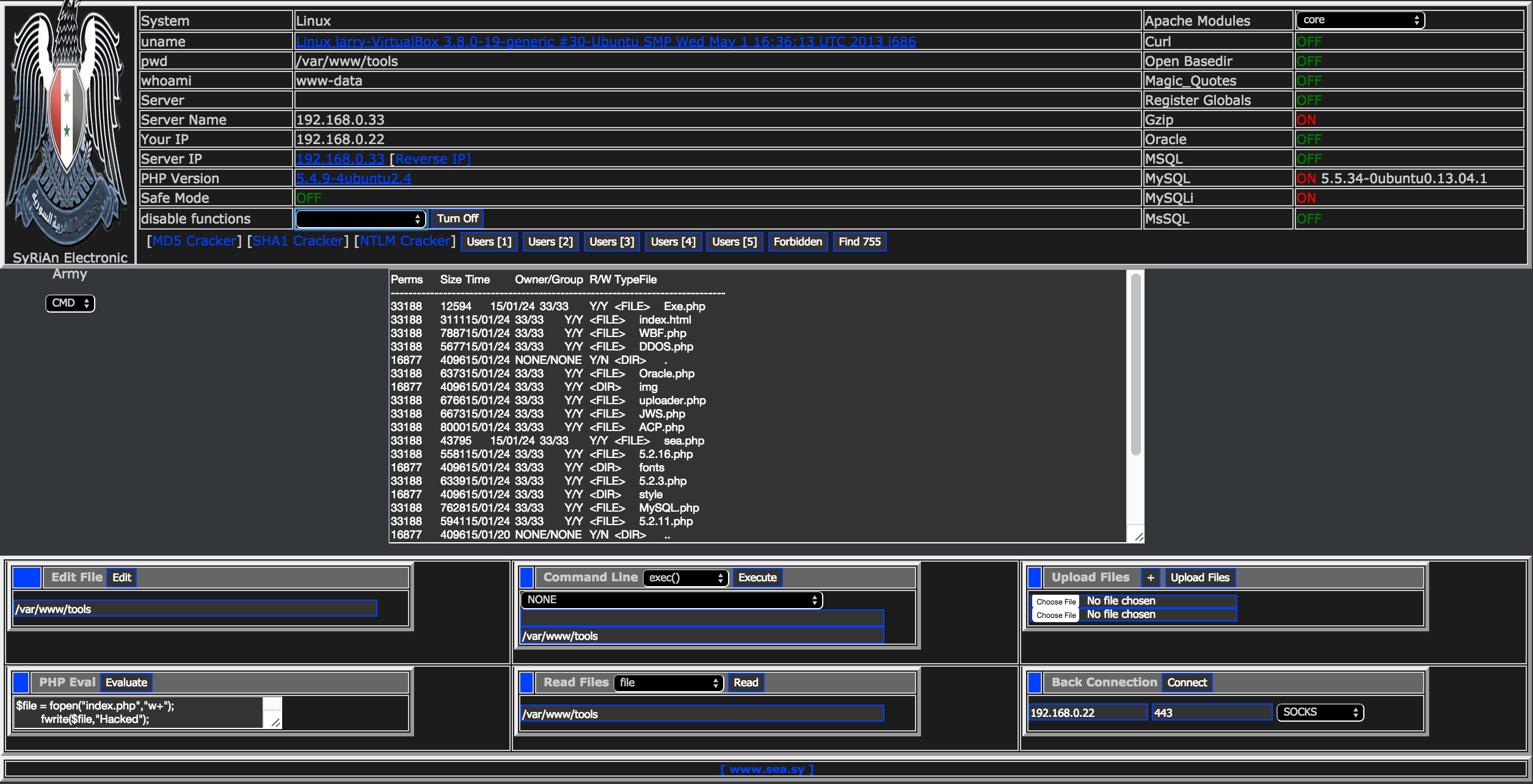
The apache webserver listening on 0.0.0.0:80 allowing remote access to all of the tools in their catalog. These tools allow remote command execution and file uploads, it was the intent of the SEA to have these only accessable to the local user.
root@larry-VirtualBox:/etc/mysql# netstat -an
Active Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State
tcp 0 0 127.0.0.1:6010 0.0.0.0:* LISTEN
tcp 0 0 127.0.0.1:3306 0.0.0.0:* LISTEN
tcp 0 0 127.0.1.1:53 0.0.0.0:* LISTEN
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN
tcp 0 0 127.0.0.1:631 0.0.0.0:* LISTEN
tcp 0 0 192.168.0.33:22 192.168.0.22:53474 ESTABLISHED
tcp6 0 0 ::1:6010 :::* LISTEN
tcp6 0 0 :::80 :::* LISTEN
tcp6 0 0 :::22 :::* LISTEN
tcp6 0 0 ::1:631 :::* LISTEN
tcp6 1 0 ::1:57375 ::1:631 CLOSE_WAIT
udp 0 0 0.0.0.0:68 0.0.0.0:*
udp 0 0 0.0.0.0:52375 0.0.0.0:*
udp 0 0 0.0.0.0:5353 0.0.0.0:*
udp 0 0 0.0.0.0:41938 0.0.0.0:*
udp 0 0 0.0.0.0:31229 0.0.0.0:*
udp 0 0 127.0.1.1:53 0.0.0.0:*
udp6 0 0 :::37598 :::*
udp6 0 0 :::5353 :::*
udp6 0 0 :::12590 :::*
udp6 0 0 :::52638 :::*
udp6 0 0 :::546 :::*
Active UNIX domain sockets (servers and established)
This apache server is a tool server hosting web based tools by the SEA
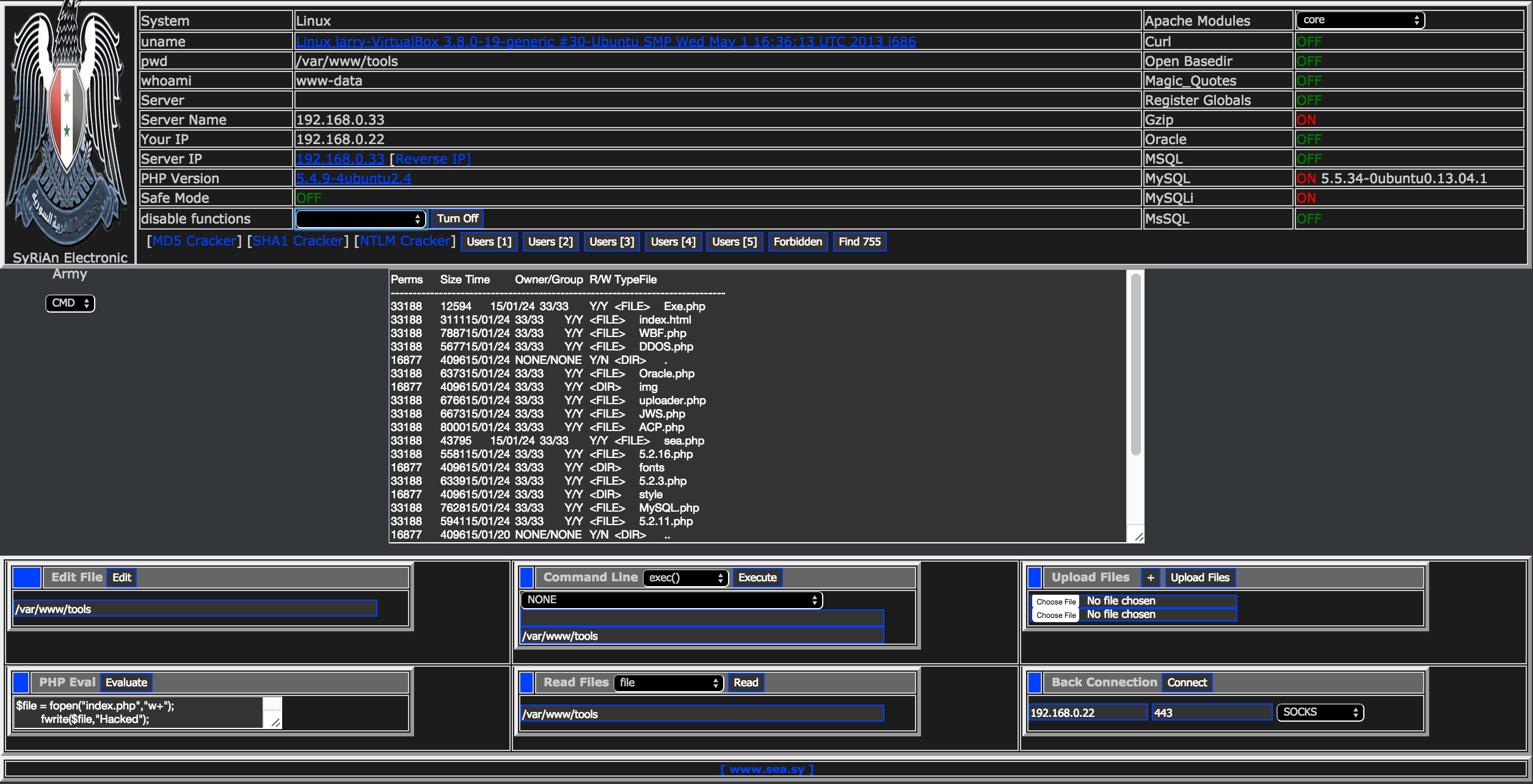
One of the tools is a web shell to the system
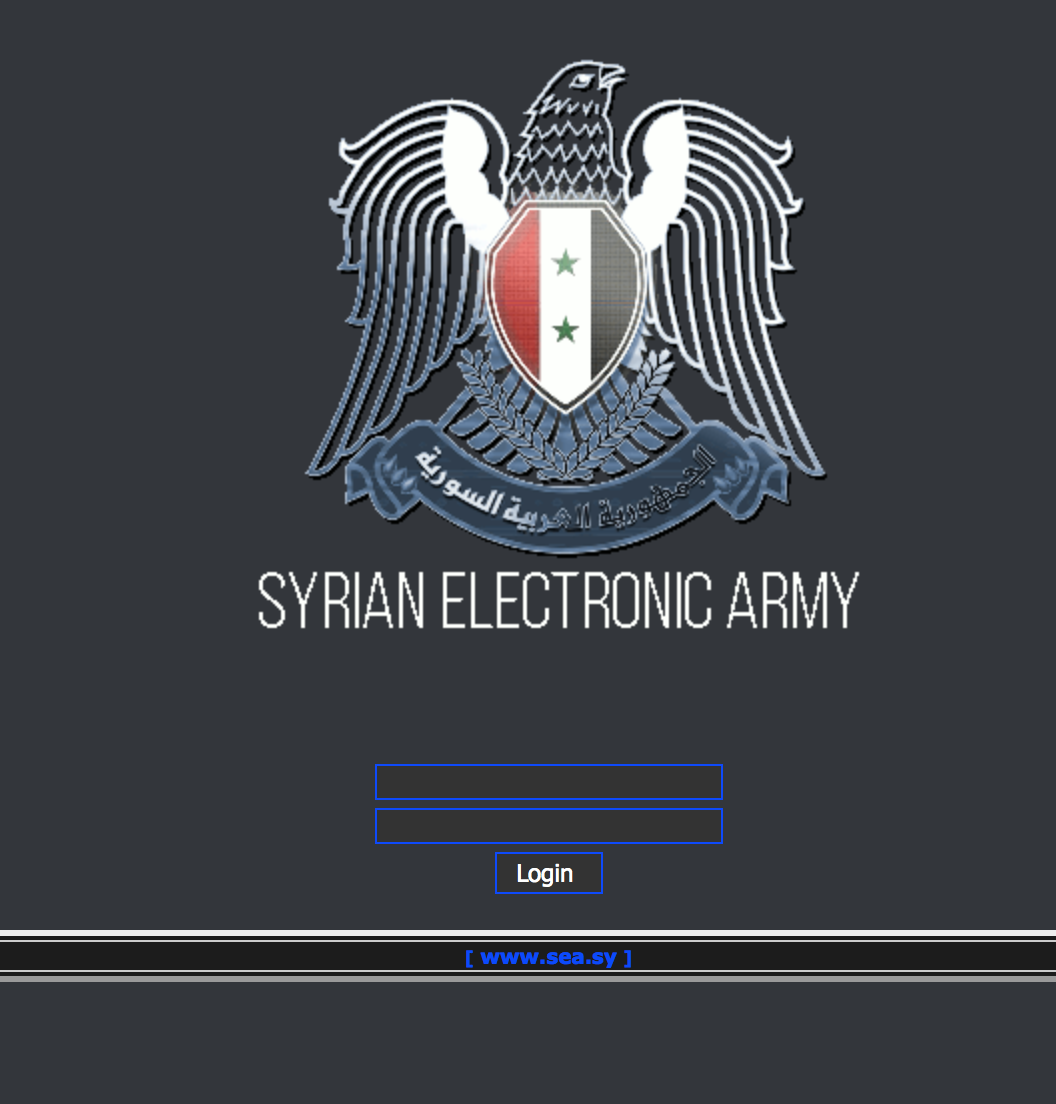
The path http://192.168.0.33/tools/sea.php is a webshell, meant to be accessable only locally but due to a misconfiguration is available remotely.
Also the path http://192.168.0.33/tools/Exe.php is also a webshell.
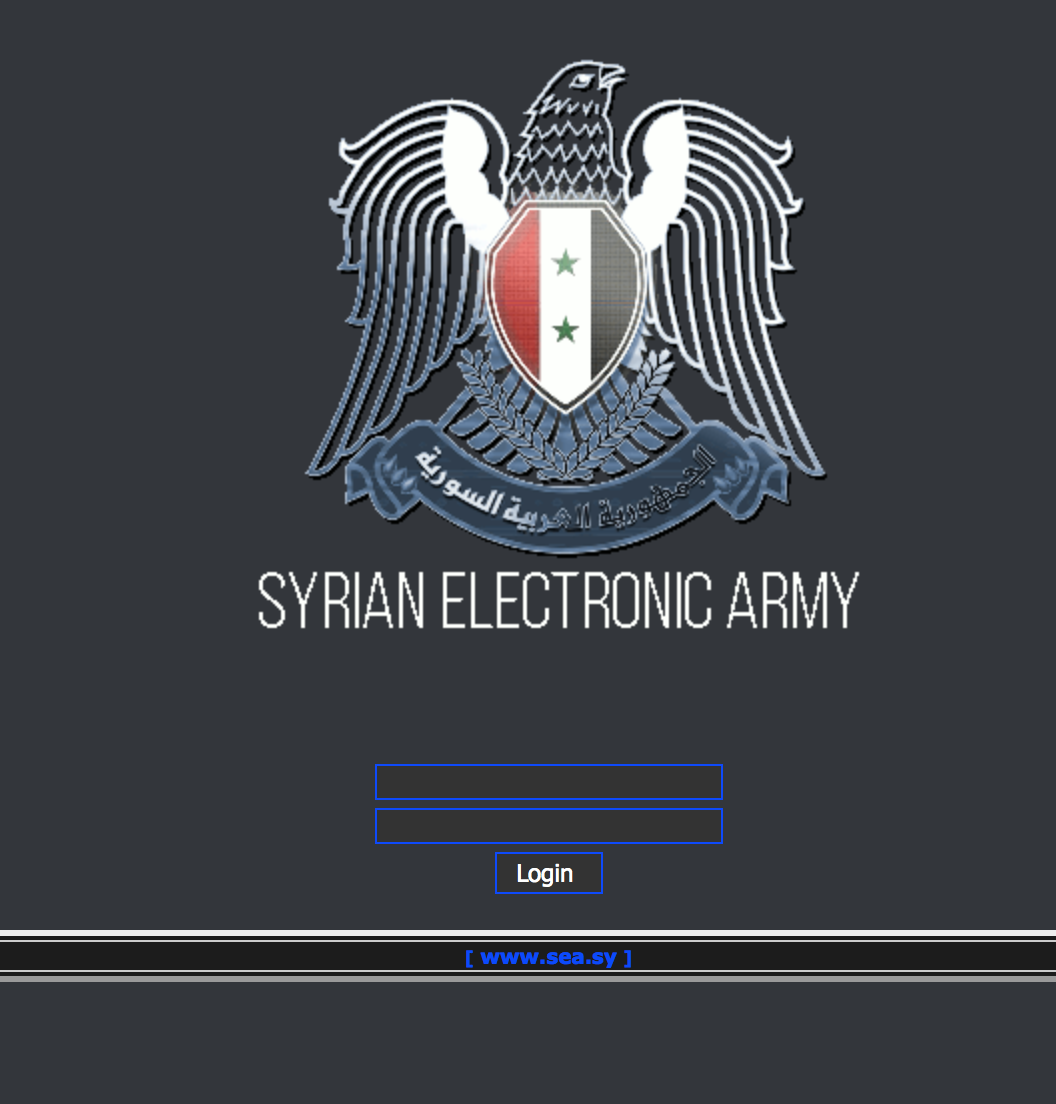
Here is a screen shot after logging in:
From lines 6-15 contain the credentials sea.php:
6 $user = 'SEA'; ^M
7 $pass = 'SEA'; ^M
8 $uselogin = 1;^M
9 $sh3llColor = "#0040FF";^M
10 ^M
11 # MySQL Info ---------^M
12 $DBhost = "localhost";^M
13 $DBuser = "root";^M
14 $DBpass = "root";^M
15 #---------------------^M
The folks over at osvdb.org assigned this ID: 117796, though it makes no mention
of the webshells available remotely on port 80.
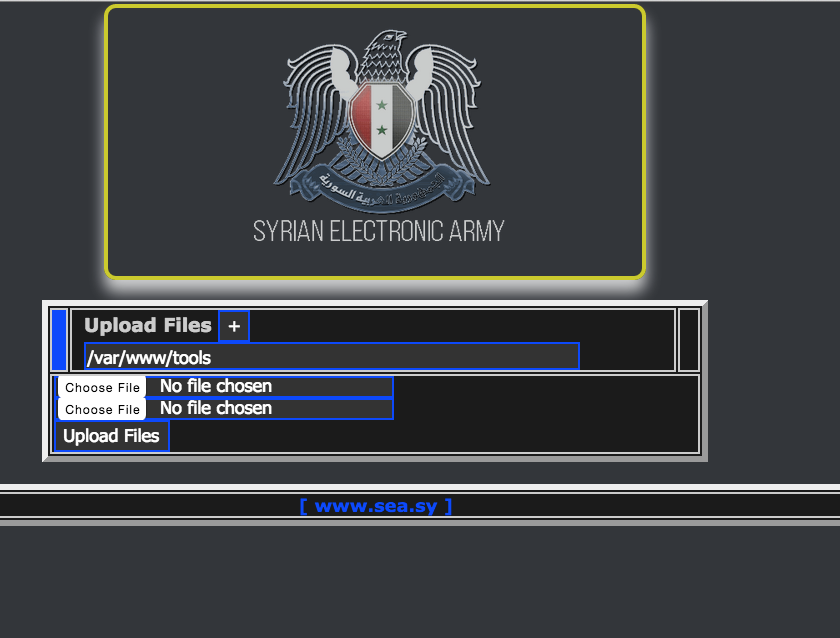
Looks like an uploader script too at http://192.168.0.33/tools/uploader.php